Woke up this morning to find out that one of our businesses website was hacked and all admin users had their emails changed. Start investigating and found that some random kid has used this scanner to check for vulnerabilities on our domain: http://01.com/esop.php
We had a small module for testimonials which had this code in it:
http://seology.com/alb-hack/blocktestimonial.txt
httpdocs/modules/blocktestimonial/blocktestimonial.php
Code: Select all
public function uploadImage(){
$uploadpath = "upload";
//upload the files
move_uploaded_file($_FILES["testimonial_img"]["tmp_name"],
_PS_ROOT_DIR_.DIRECTORY_SEPARATOR.$uploadpath.DIRECTORY_SEPARATOR.$_FILES["testimonial_img"]["name"]);
//store the path for displaying the image
$testimonial_img = $uploadpath ."/".$_FILES["testimonial_img"]["name"];
$testimonial_img = addslashes($testimonial_img);
return $testimonial_img; //return image path
}Error logs here:
http://seology.com/alb-hack/199err.txt
Access logs here:
http://seology.com/alb-hack/199acc.txt
Uploaded files here:
http://seology.com/alb-hack/uploaded.tar.gz
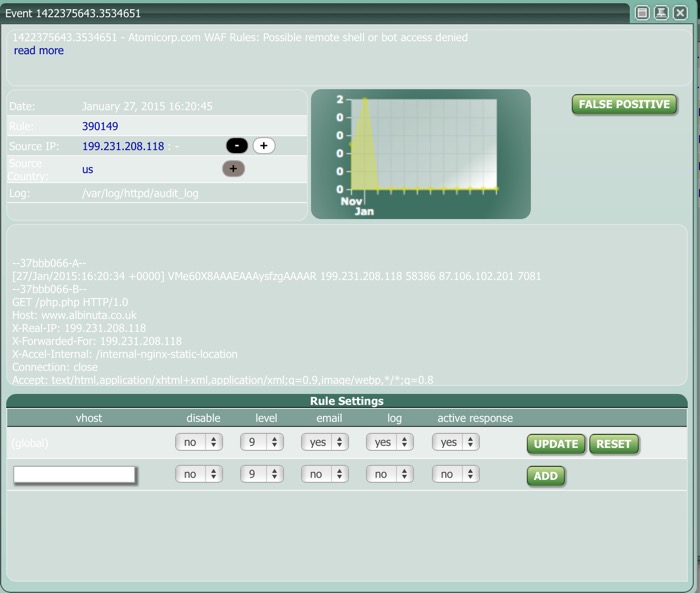
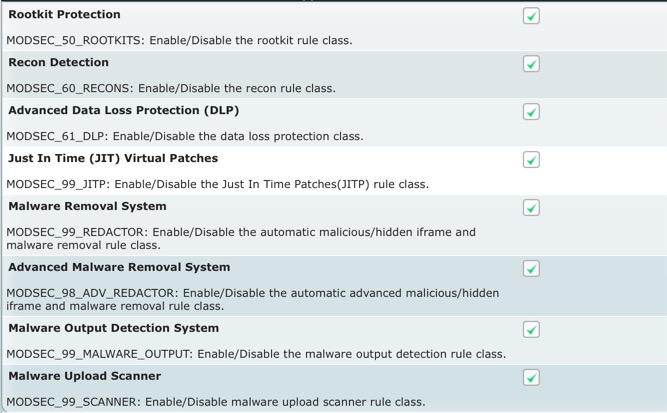
Should ASL not pick this up and block it?
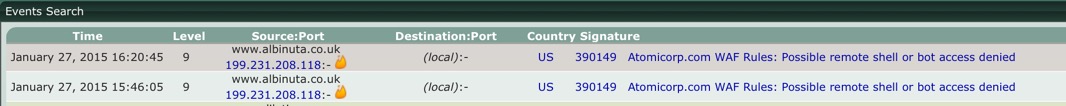
Only found this in ASL: